Fact Finder - History
Internet (TCP/IP Protocols)
Every time you send a message or stream a video, TCP/IP is working invisibly beneath the surface. You've probably never questioned how your data actually travels across the globe in milliseconds. It's a story involving Cold War military research, deliberate engineering choices, and tradeoffs that still shape your digital life today. What you're about to discover will change how you think about every connection you make.
Key Takeaways
- TCP/IP was developed by the U.S. Department of Defense in the 1970s to keep communications alive during a nuclear attack.
- Each IP address supports up to 65,535 ports, allowing thousands of simultaneous connections from a single address.
- IPv4 supports only ~4 billion addresses; IPv6 was introduced to solve exhaustion, while IPv5 was skipped entirely.
- TCP guarantees data delivery through acknowledgments and retransmissions; UDP sacrifices reliability for speed.
- Routers never inspect application payloads — they forward packets purely based on IP header addressing information.
What Is TCP/IP and Why Does Every Internet Connection Need It?
Every internet connection you make relies on two foundational protocols working in tandem: the Transmission Control Protocol (TCP) and the Internet Protocol (IP). TCP handles reliable data delivery, while IP manages addressing and routing. Together, they form a network abstraction layer between your applications and the underlying infrastructure, enabling application interoperability across virtually any operating system or hardware.
Developed by the U.S. Department of Defense in the 1970s, TCP/IP isn't controlled by any single company, making it universally compatible. Without it, your device can't communicate over the internet. It powers everything you use online — the web, email, file transfers, and streaming. The protocols and related standards are now maintained by the IETF.
Every packet you send gets routed, tracked, and verified through this protocol suite, ensuring your data arrives accurately and in the correct order. The model itself is structured into five distinct layers, each responsible for a specific function in the transmission process. For those wanting to explore protocol-related data and categories further, online fact-finding tools can surface concise, organized information across subjects like science and technology.
TCP/IP Was Born From a Cold War Problem
But where did TCP/IP actually come from? It started with Cold War fears. In the late 1960s, the U.S. Department of Defense worried that nuclear attacks could destroy centralized communication systems, leaving the military with no way to coordinate. They needed survivable networks that could keep functioning even after taking serious damage.
That fear drove ARPA to fund ARPANET, using packet switching pioneered by Paul Baran. Instead of relying on a single central hub, data traveled in independent packets across multiple routes. If one path failed, packets simply found another.
This military influence shaped everything. Distributed design wasn't just a technical preference — it was a survival strategy. The Cold War problem demanded a solution flexible and resilient enough to eventually connect the entire world. DARPA researchers later developed TCP/IP to solve the problem of multiple independently built networks being unable to communicate with one another.
Before TCP/IP existed, ARPANET relied on NCP, or Network Control Protocol, which could only facilitate communication between hosts within ARPANET itself and had no ability to connect outside networks. This era of early network development paralleled other significant documentation efforts of the 20th century, such as Zora Neale Hurston's anthropological work capturing firsthand historical accounts that, like early internet protocols, were preserved in archives long before reaching a wide audience.
The Four Layers of the TCP/IP Model Explained
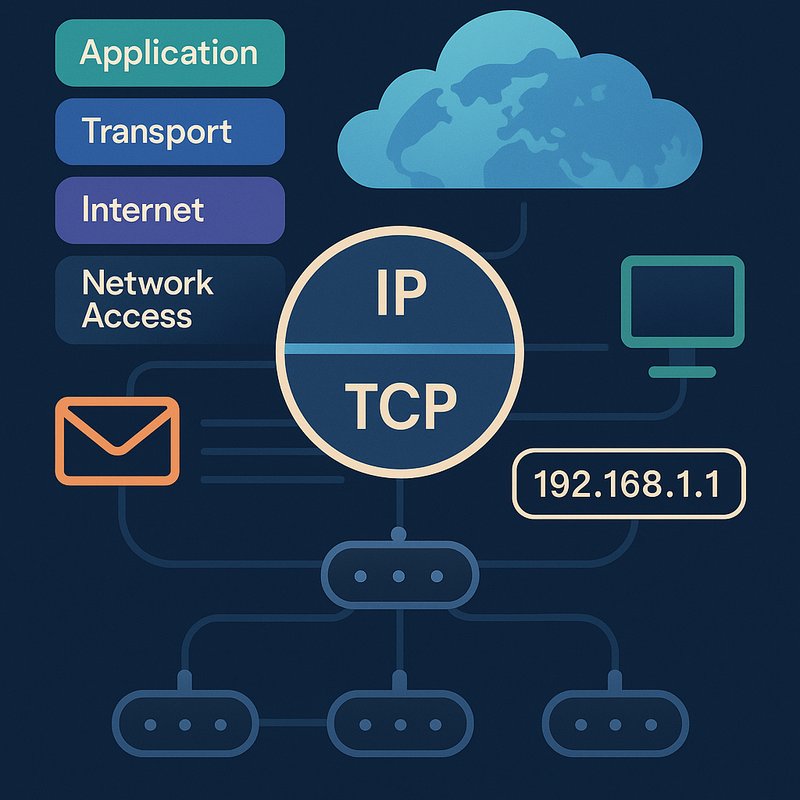
TCP/IP organizes network communication into four distinct layers, each handling a specific job so data moves reliably from one device to another.
Starting at the top, the Application layer manages protocols like HTTP, DNS, and FTP, giving your programs a way to communicate. Below it, the Transport layer handles segmentation, flow control, and error handling using TCP or UDP.
The Internet layer then packs data into IP datagrams and routes them across networks.
Finally, the Network Access layer transmits raw bits through physical hardware like Ethernet cables and network cards. Ethernet relies on CSMA/CD to manage shared-media access, where devices sense the medium before transmitting and retry after a random backoff if a collision occurs. Layer interactions happen through header structures added at each stage during transmission and stripped away in reverse during reception. This organized process guarantees your data travels efficiently across any network path.
The TCP/IP model differs from the OSI model in that it consolidates communication into four layers instead of seven, making it simpler and more widely adopted across modern networks. When coordinating communication across distributed teams or global systems, tools that offer real-time comparison of time zones can help align schedules across different network-connected locations.
What IP Addresses Actually Are and How They Work
Now that you understand how TCP/IP layers move data across a network, it helps to understand what IP addresses actually are and how they make that routing possible. An IP address is your device's digital identifier, enabling accurate data delivery across local and global networks. Dynamic addressing lets ISPs assign changing public IPs, which also affects geolocation privacy. IPv6 was designed to skip version 5, as that number was already assigned to the experimental Internet Stream Protocol. Static IPs, by contrast, remain constant and are commonly assigned by ISPs for servers and hosting.
Here's what you should know:
- IPv4 uses four decimal octets (0–255), supporting ~4 billion addresses
- IPv6 uses eight hexadecimal groups, providing trillions of unique addresses
- Public IPs are internet-facing; private IPs handle internal network communication
- NAT translates private addresses to public for outbound internet traffic
- Packet headers carry source and destination IPs so routers forward data correctly
How TCP/IP Breaks Your Data Into Packets and Routes It?
When you send a message or load a webpage, TCP breaks your data into smaller packets at the transport layer, tagging each with a sequence number so they can be reassembled in order at the destination.
Each packet gets source and destination IP addresses for routing across the network.
Routers forward packets using routing tables, and since packets travel independently, route convergence determines how quickly routers agree on the best available paths.
The TTL field prevents lost packets from circulating indefinitely by decrementing at each hop.
If a packet exceeds a network's MTU, IP handles packet fragmentation, splitting it into smaller units that the receiving system later reassembles using offset fields.
TCP then confirms delivery through acknowledgments, retransmitting anything lost and verifying integrity with checksums.
ICMP plays a supporting role in this process, reporting critical network errors such as dropped packets and unreachable destinations back to the sending system.
This entire system supports everything from web browsing and email to file transfers and streaming, making TCP/IP the foundation of modern network communication worldwide.
TCP vs. UDP: Why the Internet Uses Both
Once TCP has broken your data into packets and confirmed their delivery, another question arises: does every application actually need that level of reliability? Not always. That's why the internet uses both TCP and UDP, each handling different needs through port multiplexing.
Here's what separates them:
- TCP guarantees delivery using acknowledgements and retransmissions, preventing packet fragmentation loss
- UDP skips connection setup entirely, sending data immediately without waiting for agreements
- TCP reorders out-of-sequence packets; UDP delivers them however they arrive
- TCP's variable 20–60 byte header adds overhead; UDP's fixed 8-byte header keeps things lean
- TCP suits file transfers and web browsing; UDP powers gaming, streaming, and voice calls
You need both because reliability and speed serve completely different purposes depending on what you're transmitting. Unlike TCP, UDP supports broadcasting and multicasting, making it well suited for scenarios where data must reach multiple destinations simultaneously. On the security side, TCP's three-way handshake offers some protection against forged IP addresses, while UDP's connectionless nature leaves it more exposed to spoofing and denial of service attacks.
The TCP/IP Three-Way Handshake Behind Every Connection
Before any data moves between your device and a server, TCP runs a three-step ritual called the three-way handshake.
First, your device sends a SYN segment containing its Initial Sequence Number, signaling a connection request.
Second, the server replies with a SYN-ACK, acknowledging your SYN while sharing its own sequence number.
This exchange drives sequence synchronization, ensuring both sides know exactly where each other's data stream begins.
Third, your device sends a final ACK, confirming the server's sequence number and pushing both endpoints into the ESTABLISHED state.
Beyond organizing data flow, this process strengthens handshake security by verifying that both parties are reachable and ready before transmission begins.
If any segment gets lost, TCP retransmits it, keeping the connection reliable from the start. This retransmission behavior is part of Positive Acknowledgement with Retransmission, a core reliability mechanism where every sent segment must be acknowledged before the sender considers it successfully delivered.
The transport layer also uses a checksum for error detection, ensuring that any damaged segments are silently discarded rather than processed as valid data.
Why TCP/IP Won When Every Other Protocol Failed
TCP/IP didn't win by accident—it earned its place by doing what every competing protocol couldn't: scale, adapt, and stay open. Its design philosophy placed intelligence at the edges, not the core, slashing overhead while boosting flexibility. Deployment incentives were strong—it was free, open, and backed by DoD mandates that forced adoption across military and commercial networks.
Here's why it outlasted every rival:
- It neutralized X.25 by running on top of it
- IETF's open RFCs invited global developer collaboration
- CIDR and BGP handled explosive routing growth
- Van Jacobson's congestion control stabilized the entire suite
- Modular design absorbed mobile and IoT without breaking
You're using the protocol right now—and it still hasn't hit its ceiling. The entire foundation traces back to ARPANET's 1983 transition, when TCP/IP replaced the Network Control Program and locked in as the definitive standard for global networking. The protocol's origins stretch back further still, to the collaborative work of Vint Cerf and Bob Kahn, whose seminal 1974 paper addressed routing across heterogeneous networks and introduced the concept of fragmentable datagram internetworking that made TCP/IP's flexibility possible from the start.
Why TCP/IP Works the Same for Email, Streaming, and Voice Calls
Whether you're sending an email, streaming a playlist, or jumping on a video call, the same underlying protocol stack handles all of it—without modification. TCP/IP's application neutrality means IP routes your packets without caring what's inside them. The stack simply breaks data into packets, ships them across the network, and reassembles them at the destination.
What separates your email from your Spotify stream is port multiplexing. Your device assigns distinct ports to each connection—port 25 handles SMTP email while RTP over UDP manages your audio stream. TCP guarantees your email arrives ordered and intact; UDP prioritizes speed for voice and video where minor packet loss beats frustrating delays. Same stack, same routing framework, different transport choices—each protocol adapts without changing the foundation underneath. Each IP address supports up to 65,535 ports, giving your device the capacity to manage countless simultaneous connections across every application running at once.
Modern protocols like WebRTC and SRT run over UDP but layer on application-level reliability additions, recovering from packet loss without sacrificing the low latency that makes real-time communication feel immediate.
How TCP/IP's Open Design Creates Modern Cybersecurity Challenges
The same open design that makes TCP/IP universally flexible also leaves it structurally exposed. Off-path attackers don't need direct access to your traffic—they exploit cross-layer weaknesses using ICMP error injection to manipulate TCP behavior and leak sensitive sequence numbers. Source spoofing lets attackers forge packet origins, bypassing authentication entirely.
You're vulnerable through multiple attack vectors:
- Open ports on legacy services lack authentication and encryption
- ICMP manipulation enables off-path TCP hijacking without packet interception
- Source spoofing forges IP addresses, deceiving network controls
- SYN floods exhaust connection queues within seconds
- Web protocols remain exposed to injection attacks despite encryption
These aren't recent oversights—they've persisted across 40+ years of development, threatening core Internet infrastructure daily. Port scanning helps organizations identify which of these exposures are actively listening on their networks before attackers do. The TCP/IP protocol suite underpins every layer of Internet communication, meaning vulnerabilities discovered at one layer can cascade upward to affect transport and application-level protocols alike.